Nearly one million computers worldwide fell victim to a sprawling cyberattack last month that exploited an unlikely combination: people looking for free movies and the trusted software platform GitHub.
Microsoft’s threat intelligence team disclosed the campaign in December 2024, describing an operation that turned websites hosting pirated content into traps for unsuspecting users. The attack represented a troubling evolution in how cybercriminals distribute malware by hiding in plain sight on legitimate platforms.
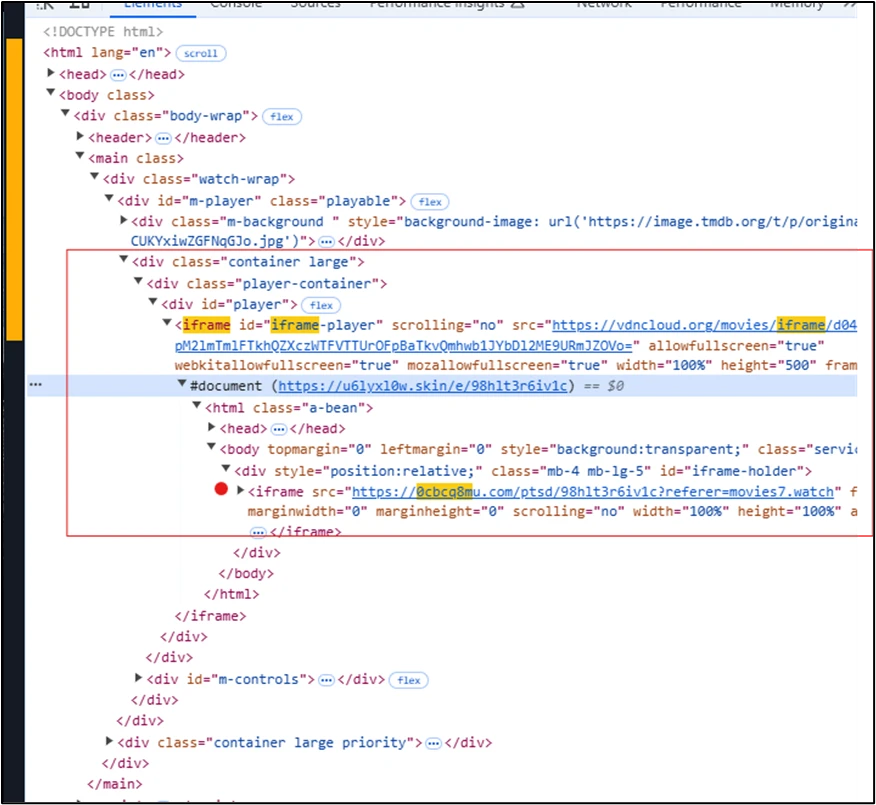
The scheme worked like this: Someone searching for a free stream of the latest blockbuster would land on an illegal streaming site. But embedded in those sites were malicious advertisements that quietly redirected visitors through a chain of websites before depositing them on GitHub, where attackers had uploaded software that appeared benign but contained dangerous payloads.
Users who downloaded and ran these files handed over access to their computers. The malware quickly got to work cataloging system information and installing additional programs, including Lumma, a tool designed to steal passwords and financial data. The attackers also deployed an updated variant of Doenerium and used NetSupport, a legitimate remote access program typically used by IT departments, to maintain control of infected machines.
The broad targeting meant the campaign hit both home computers and corporate networks across multiple industries. Security researchers say using GitHub complicates detection efforts because the platform hosts millions of legitimate software projects, making it harder for security tools to distinguish between safe and malicious files.
Microsoft did not identify the attackers or specify which countries saw the highest infection rates. The company’s disclosure comes as cybersecurity experts have grown increasingly concerned about malvertising, a technique that has proven effective because it requires no special action from victims beyond visiting a compromised website.
For users, the incident offers a reminder that piracy sites carry risks beyond legal trouble. Security experts recommend sticking to legitimate streaming services and keeping antivirus software up to date. Organizations should block access to known piracy domains on corporate networks and train employees to recognize suspicious download requests.
The attackers’ decision to weaponize GitHub highlights how cybercriminals adapt their methods to exploit trust in widely used platforms, making traditional security approaches less effective.
Recommendations and Mitigation
To mitigate the risks associated with such attacks, organizations and individuals are advised to:
- Exercise Caution: Avoid visiting illegal streaming sites or downloading content from untrusted sources.
- Implement Security Measures: Use reputable security software and ensure it is regularly updated to detect and prevent malware.
- Educate Users: Conduct regular training sessions to raise awareness about the dangers of malvertising and the importance of safe browsing habits.
By staying vigilant and adopting proactive security practices, users can protect themselves against such sophisticated cyber threats.

